Component: ssosync
Deploys AWS ssosync to sync Google Groups with AWS SSO.
AWS ssosync is a Lambda application that regularly manages Identity Store users.
This component requires manual deployment by a privileged user because it deploys a role in the root or identity management account.
Usage
You should be able to deploy the ssosync component to the same account as aws-sso. Typically that is the core-gbl-root or gbl-root stack.
Stack Level: Global Deployment: Must be deployed by managers team-member or SuperAdmin using atmos CLI (since this is a root account deployment). This could also be deployed in an identity management account.
The following is an example snippet for how to use this component:
(stacks/catalog/aws-ssosync.yaml)
components:
terraform:
ssosync:
vars:
enabled: true
name: ssosync
google_admin_email: [email protected]
log_format: text
log_level: warn
schedule_expression: "rate(15 minutes)"
# Filter the groups that will be synced and is optional (default: all groups)
# This supports wild cards `*`
google_group_match:
- "email='[email protected]'"
- "email='[email protected]'"
- "name='Acme Team'"
We recommend following a similar process to what the AWS ssosync documentation recommends.
Deployment
Overview of steps:
- Configure AWS IAM Identity Center
- Configure Google Cloud console
- Configure Google Admin console
- Deploy the
aws-ssosynccomponent - Deploy the
aws-ssocomponent
1. Configure AWS IAM Identity Center (AWS SSO)
Follow AWS documentation to configure SAML and SCIM with Google Workspace and IAM Identity Center. Do steps 1-4. Step 5: Google Workspace: Configure auto provisioning is impossible.
As part of this process, save the SCIM endpoint token and URL. Then in AWS SSM Parameter Store, create two
SecureString parameters in the same account used for AWS SSO. This is usually the root account in the primary region.
These can be found by clicking Enable Automatic provisioning in the AWS IAM Identity Center console.
# Typically looks like `https://scim.us-east-2.amazonaws.com/.../scim/v2`
/ssosync/scim_endpoint_url
# Typically looks like a base64 encoded value
/ssosync/scim_endpoint_access_token
Select Settings, under the Identity Source section, copy the Identity Store ID and create the following parameter:
# Typically looks like `d-000000aaaa`
/ssosync/identity_store_id
2. Configure Google Cloud console
Within the Google Cloud console, we need to create a new Google Project and Service Account and enable the Admin SDK API. Follow these steps:
- Create a new project. Give the project a descriptive name such as
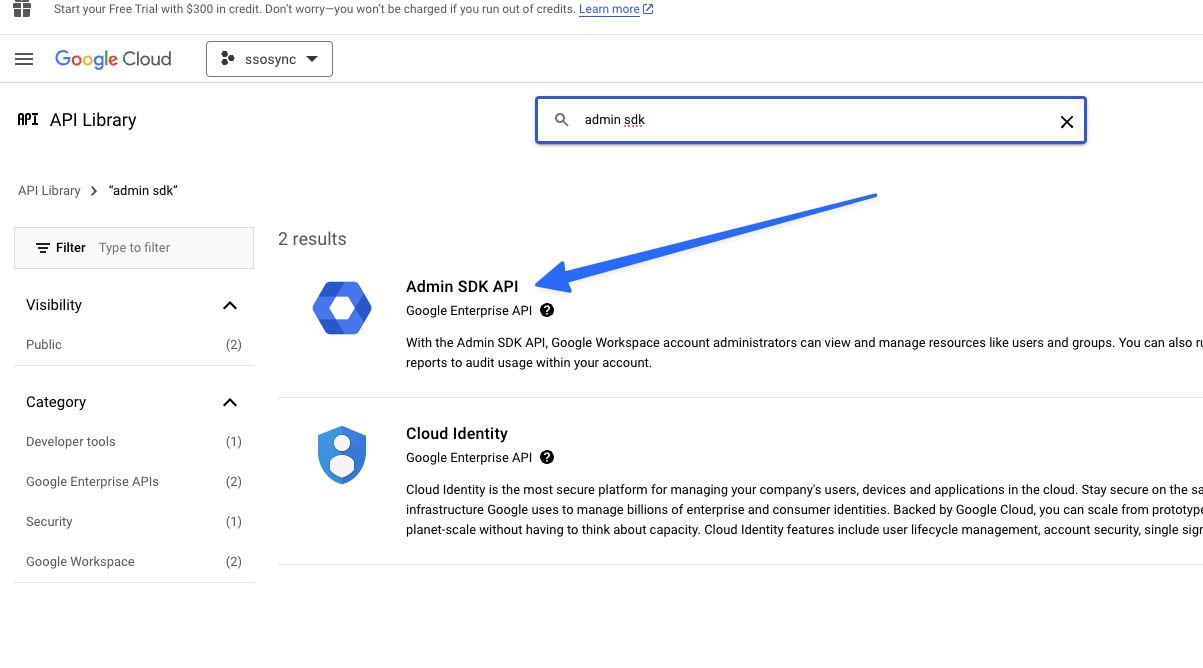
AWS SSO Sync - Enable Admin SDK in APIs:
APIs & Services > Enabled APIs & Services > + ENABLE APIS AND SERVICES
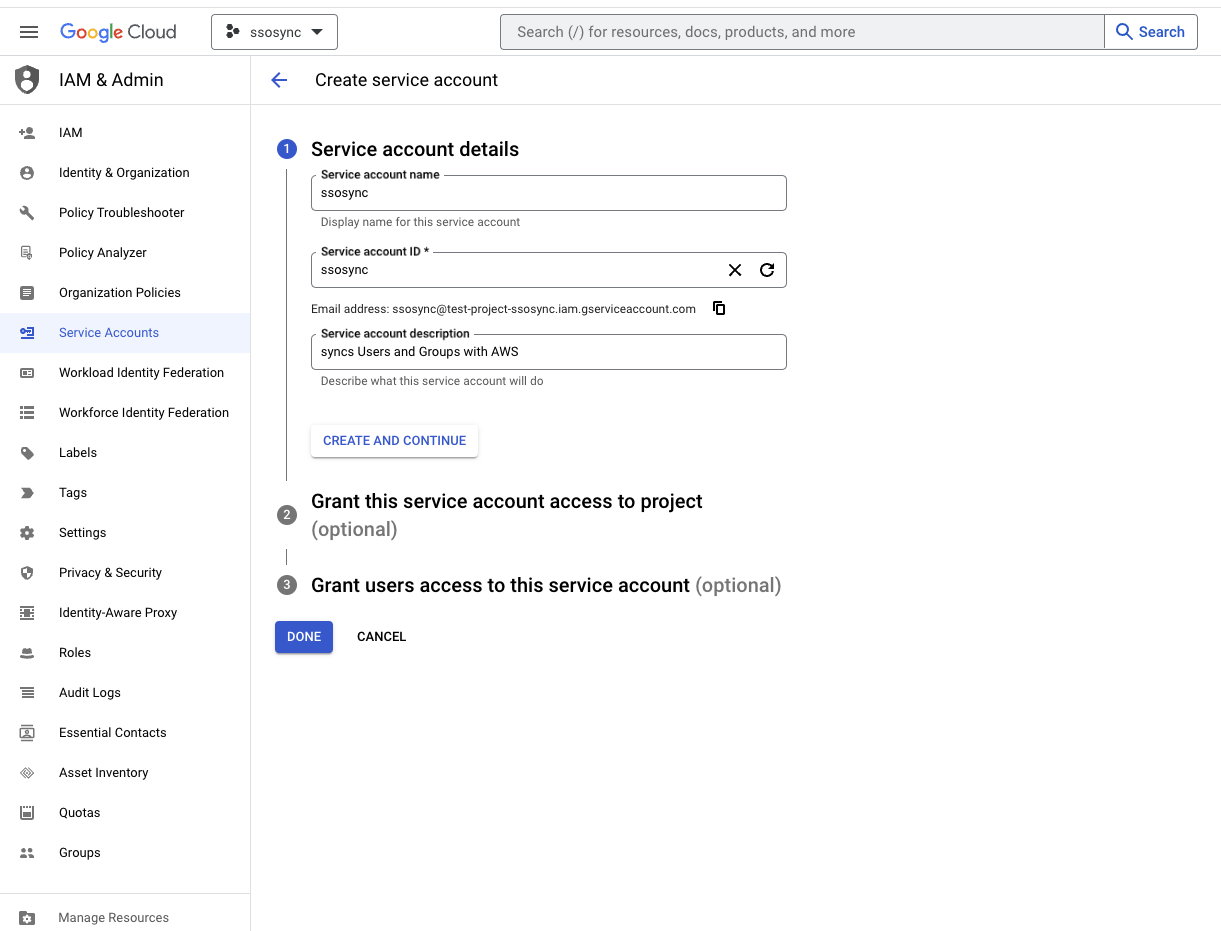
- Create Service Account:
IAM & Admin > Service Accounts > Create Service Account(ref).
- Download credentials for the new Service Account:
IAM & Admin > Service Accounts > select Service Account > Keys > ADD KEY > Create new key > JSON
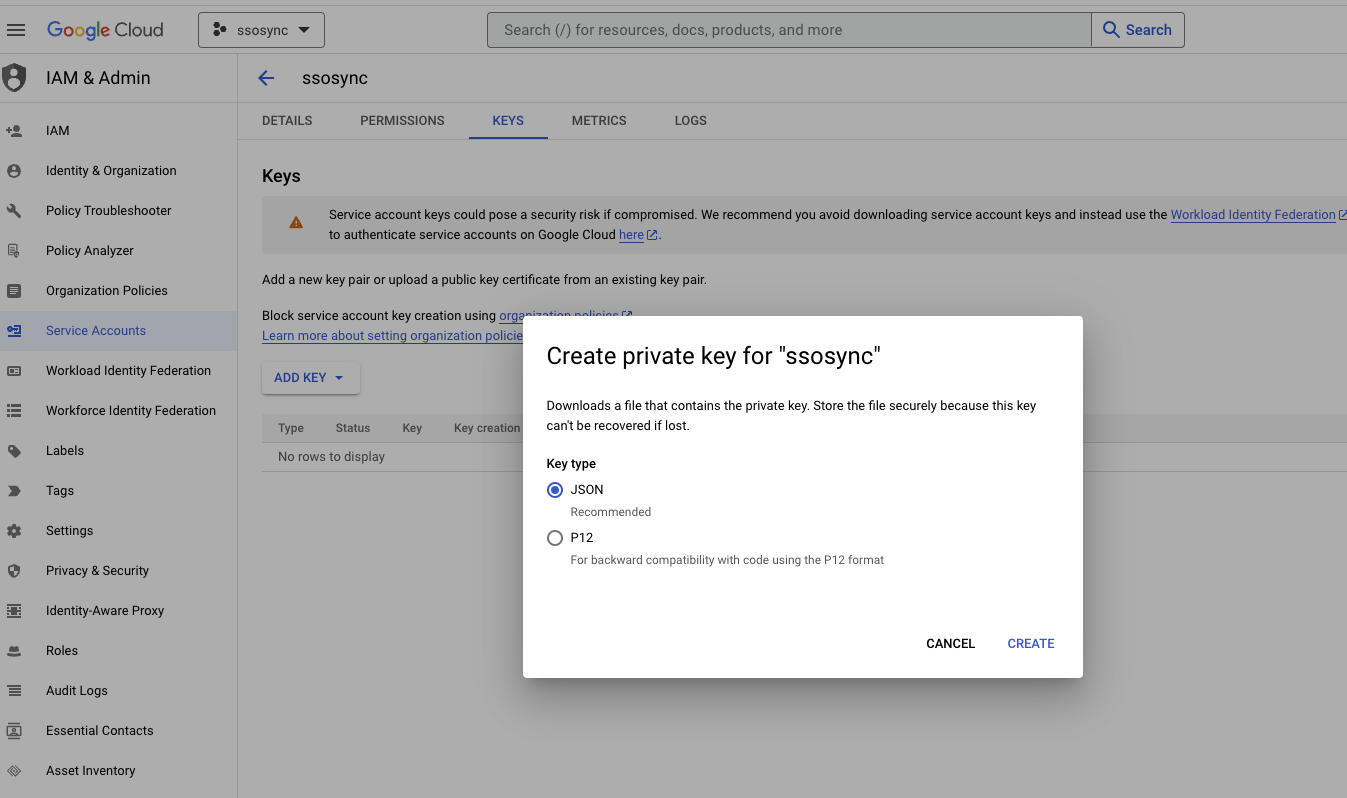 6. Save the JSON credentials as a new
6. Save the JSON credentials as a new SecureString AWS SSM parameter in the same account used for AWS SSO. Use the
full JSON string as the value for the parameter.
/ssosync/google_credentials
3. Configure Google Admin console
- Open the Google Admin console
- From your domain’s Admin console, go to
Main menu menu > Security > Access and data control > API controls - In the Domain wide delegation pane, select
Manage Domain Wide Delegation. - Click
Add new. - In the Client ID field, enter the
Unique IDof the Service Account created in step 2, this should be a 22 number string. - In the OAuth Scopes field, enter
https://www.googleapis.com/auth/admin.directory.group.readonly,https://www.googleapis.com/auth/admin.directory.group.member.readonly,https://www.googleapis.com/auth/admin.directory.user.readonly
4. Deploy the aws-ssosync component
Make sure that all four of the following SSM parameters exist in the target account and region:
/ssosync/scim_endpoint_url/ssosync/scim_endpoint_access_token/ssosync/identity_store_id/ssosync/google_credentials
If deployed successfully, Groups and Users should be programmatically copied from the Google Workspace into AWS IAM Identity Center on the given schedule.
If these Groups are not showing up, check the CloudWatch logs for the new Lambda function and refer the FAQs included below.
5. Deploy the aws-sso component
Use the names of the Groups now provisioned programmatically in the aws-sso component catalog. Follow the
aws-sso component documentation to deploy the aws-sso component.
FAQ
Why is the tool forked by Benbentwo?
The awslabs tool requires AWS Secrets Managers for the Google Credentials. However, we would prefer to use AWS SSM to
store all credentials consistency and not require AWS Secrets Manager. Therefore we've created a Pull Request and will
point to a fork until the PR is merged.
Ref:
What should I use for the Google Admin Email Address?
The Service Account created will assume the User given by --google-admin / SSOSYNC_GOOGLE_ADMIN /
var.google_admin_email. Therefore, this user email must be a valid Google admin user in your organization.
This is not the same email as the Service Account.
If Google fails to query Groups, you may see the following error:
Notifying Lambda and mark this execution as Failure: googleapi: Error 404: Domain not found., notFound
Common Group Name Query Error
If filtering group names using query strings, make sure the provided string is valid. For example,
google_group_match: "name:aws*" is incorrect. Instead use google_group_match: "Name:aws*"
If not, you may again see the same error message:
Notifying Lambda and mark this execution as Failure: googleapi: Error 404: Domain not found., notFound
Ref:
The specific error you are seeing is because the google api doesn't like the query string you provided for the -g parameter. try -g "Name:Fuel*"
https://github.com/awslabs/ssosync/issues/91
Variables
Required Variables
google_admin_email(string) requiredGoogle Admin email
region(string) requiredAWS Region where AWS SSO is enabled
Optional Variables
architecture(string) optionalArchitecture of the Lambda function
Default value:
"x86_64"google_credentials_ssm_path(string) optionalSSM Path for
ssosyncsecretsDefault value:
"/ssosync"google_group_match(list(string)) optionalGoogle Workspace group filter query parameter, example: 'name:Admin* email:aws-*', see: https://developers.google.com/admin-sdk/directory/v1/guides/search-groups
Default value:
[ ]google_user_match(list(string)) optionalGoogle Workspace user filter query parameter, example: 'name:John* email:admin*', see: https://developers.google.com/admin-sdk/directory/v1/guides/search-users
Default value:
[ ]ignore_groups(string) optionalIgnore these Google Workspace groups
Default value:
""ignore_users(string) optionalIgnore these Google Workspace users
Default value:
""include_groups(string) optionalInclude only these Google Workspace groups. (Only applicable for sync_method user_groups)
Default value:
""log_format(string) optionalLog format for Lambda function logging
Default value:
"json"log_level(string) optionalLog level for Lambda function logging
Default value:
"warn"schedule_expression(string) optionalSchedule for trigger the execution of ssosync (see CloudWatch schedule expressions)
Default value:
"rate(15 minutes)"ssosync_url_prefix(string) optionalURL prefix for ssosync binary
Default value:
"https://github.com/cloudposse/ssosync/releases/download"ssosync_version(string) optionalVersion of ssosync to use
Default value:
"v3.0.0"sync_method(string) optionalSync method to use
Default value:
"groups"
Context Variables
The following variables are defined in the context.tf file of this module and part of the terraform-null-label pattern.
context.tf file of this module and part of the terraform-null-label pattern.additional_tag_map(map(string)) optionalAdditional key-value pairs to add to each map in
tags_as_list_of_maps. Not added totagsorid.
This is for some rare cases where resources want additional configuration of tags
and therefore take a list of maps with tag key, value, and additional configuration.Required: No
Default value:
{ }attributes(list(string)) optionalID element. Additional attributes (e.g.
workersorcluster) to add toid,
in the order they appear in the list. New attributes are appended to the
end of the list. The elements of the list are joined by thedelimiter
and treated as a single ID element.Required: No
Default value:
[ ]context(any) optionalSingle object for setting entire context at once.
See description of individual variables for details.
Leave string and numeric variables asnullto use default value.
Individual variable settings (non-null) override settings in context object,
except for attributes, tags, and additional_tag_map, which are merged.Required: No
Default value:
{
"additional_tag_map": {},
"attributes": [],
"delimiter": null,
"descriptor_formats": {},
"enabled": true,
"environment": null,
"id_length_limit": null,
"label_key_case": null,
"label_order": [],
"label_value_case": null,
"labels_as_tags": [
"unset"
],
"name": null,
"namespace": null,
"regex_replace_chars": null,
"stage": null,
"tags": {},
"tenant": null
}delimiter(string) optionalDelimiter to be used between ID elements.
Defaults to-(hyphen). Set to""to use no delimiter at all.Required: No
Default value:
nulldescriptor_formats(any) optionalDescribe additional descriptors to be output in the
descriptorsoutput map.
Map of maps. Keys are names of descriptors. Values are maps of the form
\{<br/> format = string<br/> labels = list(string)<br/> \}
(Type isanyso the map values can later be enhanced to provide additional options.)
formatis a Terraform format string to be passed to theformat()function.
labelsis a list of labels, in order, to pass toformat()function.
Label values will be normalized before being passed toformat()so they will be
identical to how they appear inid.
Default is{}(descriptorsoutput will be empty).Required: No
Default value:
{ }enabled(bool) optionalSet to false to prevent the module from creating any resources
Required: NoDefault value:
nullenvironment(string) optionalID element. Usually used for region e.g. 'uw2', 'us-west-2', OR role 'prod', 'staging', 'dev', 'UAT'
Required: NoDefault value:
nullid_length_limit(number) optionalLimit
idto this many characters (minimum 6).
Set to0for unlimited length.
Set tonullfor keep the existing setting, which defaults to0.
Does not affectid_full.Required: No
Default value:
nulllabel_key_case(string) optionalControls the letter case of the
tagskeys (label names) for tags generated by this module.
Does not affect keys of tags passed in via thetagsinput.
Possible values:lower,title,upper.
Default value:title.Required: No
Default value:
nulllabel_order(list(string)) optionalThe order in which the labels (ID elements) appear in the
id.
Defaults to ["namespace", "environment", "stage", "name", "attributes"].
You can omit any of the 6 labels ("tenant" is the 6th), but at least one must be present.Required: No
Default value:
nulllabel_value_case(string) optionalControls the letter case of ID elements (labels) as included in
id,
set as tag values, and output by this module individually.
Does not affect values of tags passed in via thetagsinput.
Possible values:lower,title,upperandnone(no transformation).
Set this totitleand setdelimiterto""to yield Pascal Case IDs.
Default value:lower.Required: No
Default value:
nulllabels_as_tags(set(string)) optionalSet of labels (ID elements) to include as tags in the
tagsoutput.
Default is to include all labels.
Tags with empty values will not be included in thetagsoutput.
Set to[]to suppress all generated tags.
Notes:
The value of thenametag, if included, will be theid, not thename.
Unlike othernull-labelinputs, the initial setting oflabels_as_tagscannot be
changed in later chained modules. Attempts to change it will be silently ignored.Required: No
Default value:
[
"default"
]name(string) optionalID element. Usually the component or solution name, e.g. 'app' or 'jenkins'.
This is the only ID element not also included as atag.
The "name" tag is set to the fullidstring. There is no tag with the value of thenameinput.Required: No
Default value:
nullnamespace(string) optionalID element. Usually an abbreviation of your organization name, e.g. 'eg' or 'cp', to help ensure generated IDs are globally unique
Required: NoDefault value:
nullregex_replace_chars(string) optionalTerraform regular expression (regex) string.
Characters matching the regex will be removed from the ID elements.
If not set,"/[^a-zA-Z0-9-]/"is used to remove all characters other than hyphens, letters and digits.Required: No
Default value:
nullstage(string) optionalID element. Usually used to indicate role, e.g. 'prod', 'staging', 'source', 'build', 'test', 'deploy', 'release'
Required: NoDefault value:
nulltags(map(string)) optionalAdditional tags (e.g.
{'BusinessUnit': 'XYZ'}).
Neither the tag keys nor the tag values will be modified by this module.Required: No
Default value:
{ }tenant(string) optionalID element (Rarely used, not included by default). A customer identifier, indicating who this instance of a resource is for
Required: NoDefault value:
null
Outputs
arnARN of the lambda function
invoke_arnInvoke ARN of the lambda function
qualified_arnARN identifying your Lambda Function Version (if versioning is enabled via publish = true)
ssosync_artifact_urlURL of the ssosync artifact
Dependencies
Requirements
terraform, version:>= 1.0.0archive, version:>= 2.3.0aws, version:>= 4.0, < 6.0.0null, version:>= 3.0random, version:>= 1.4.1
Providers
archive, version:>= 2.3.0aws, version:>= 4.0, < 6.0.0null, version:>= 3.0random, version:>= 1.4.1
Modules
| Name | Version | Source | Description |
|---|---|---|---|
iam_roles | latest | ../account-map/modules/iam-roles | n/a |
ssosync_artifact | 0.8.0 | cloudposse/module-artifact/external | This module is the resource that actually downloads the artifact from GitHub as a tar.gz |
this | 0.25.0 | cloudposse/label/null | n/a |
Resources
The following resources are used by this module:
archive_file.lambda(resource)aws_cloudwatch_event_rule.ssosync(resource)aws_cloudwatch_event_target.ssosync(resource)aws_iam_role.default(resource)aws_lambda_function.ssosync(resource)aws_lambda_permission.allow_cloudwatch_execution(resource)null_resource.extract_my_tgz(resource)random_pet.zip_recreator(resource)
Data Sources
The following data sources are used by this module:
aws_iam_policy_document.ssosync_lambda_assume_role(data source)aws_iam_policy_document.ssosync_lambda_identity_center(data source)aws_ssm_parameter.google_credentials(data source)aws_ssm_parameter.identity_store_id(data source)aws_ssm_parameter.scim_endpoint_access_token(data source)aws_ssm_parameter.scim_endpoint_url(data source)