Module: multi-az-subnets
Terraform module for multi-AZ subnets provisioning.
The module creates private and public subnets in the provided Availability Zones.
The public subnets are routed to the Internet Gateway specified by var.igw_id.
nat_gateway_enabled flag controls the creation of NAT Gateways in the public subnets.
The private subnets are routed to the NAT Gateways provided in the var.az_ngw_ids map.
If you are creating subnets inside a VPC, consider using cloudposse/terraform-aws-dynamic-subnets instead.
Screenshots
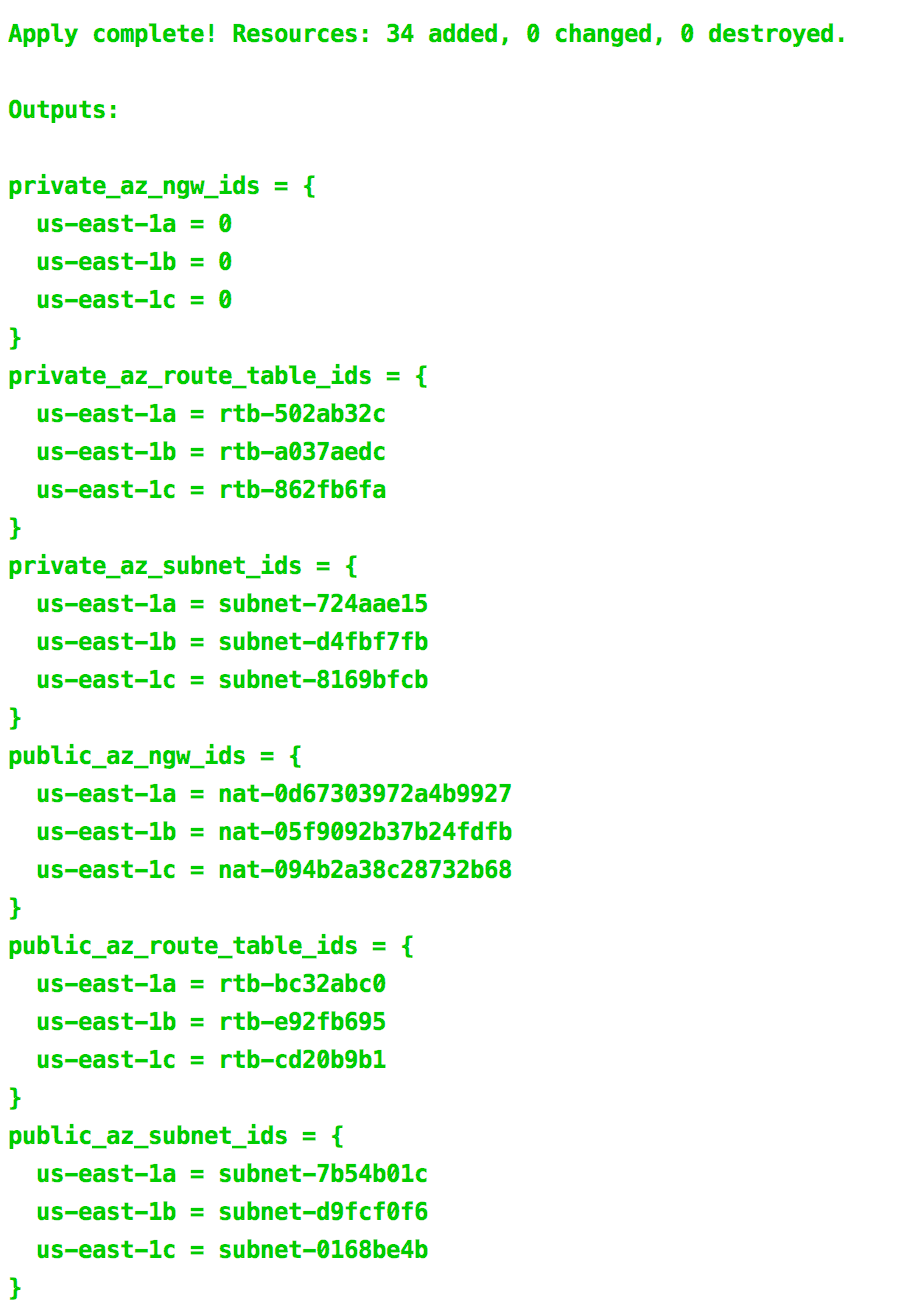 Example of
Example of terraform apply outputs
Usage
locals {
public_cidr_block = cidrsubnet(var.cidr_block, 1, 0)
private_cidr_block = cidrsubnet(var.cidr_block, 1, 1)
}
module "vpc" {
source = "cloudposse/vpc/aws"
# Cloud Posse recommends pinning every module to a specific version
# version = "x.x.x"
namespace = var.namespace
stage = var.stage
name = var.name
cidr_block = var.cidr_block
}
module "public_subnets" {
source = "cloudposse/multi-az-subnets/aws"
# Cloud Posse recommends pinning every module to a specific version
# version = "x.x.x"
namespace = var.namespace
stage = var.stage
name = var.name
availability_zones = ["us-east-2a", "us-east-2b", "us-east-2c"]
vpc_id = module.vpc.vpc_id
cidr_block = local.public_cidr_block
type = "public"
igw_id = module.vpc.igw_id
nat_gateway_enabled = "true"
}
module "private_subnets" {
source = "cloudposse/multi-az-subnets/aws"
# Cloud Posse recommends pinning every module to a specific version
# version = "x.x.x"
namespace = var.namespace
stage = var.stage
name = var.name
availability_zones = ["us-east-2a", "us-east-2b", "us-east-2c"]
vpc_id = module.vpc.vpc_id
cidr_block = local.private_cidr_block
type = "private"
az_ngw_ids = module.public_subnets.az_ngw_ids
}
Examples
Given the following configuration
module "vpc" {
source = "cloudposse/vpc/aws"
# Cloud Posse recommends pinning every module to a specific version
# version = "x.x.x"
namespace = var.namespace
name = "vpc"
stage = var.stage
cidr_block = var.cidr_block
}
locals {
public_cidr_block = cidrsubnet(module.vpc.vpc_cidr_block, 1, 0)
private_cidr_block = cidrsubnet(module.vpc.vpc_cidr_block, 1, 1)
}
module "public_subnets" {
source = "cloudposse/multi-az-subnets/aws"
# Cloud Posse recommends pinning every module to a specific version
# version = "x.x.x"
namespace = var.namespace
stage = var.stage
name = var.name
availability_zones = ["us-east-2a", "us-east-2b", "us-east-2c"]
vpc_id = module.vpc.vpc_id
cidr_block = local.public_cidr_block
type = "public"
igw_id = module.vpc.igw_id
nat_gateway_enabled = "true"
}
module "private_subnets" {
source = "cloudposse/multi-az-subnets/aws"
# Cloud Posse recommends pinning every module to a specific version
# version = "x.x.x"
namespace = var.namespace
stage = var.stage
name = var.name
availability_zones = ["us-east-2a", "us-east-2b", "us-east-2c"]
vpc_id = module.vpc.vpc_id
cidr_block = local.private_cidr_block
type = "private"
az_ngw_ids = module.public_subnets.az_ngw_ids
}
output "private_az_subnet_ids" {
value = module.private_subnets.az_subnet_ids
}
output "public_az_subnet_ids" {
value = module.public_subnets.az_subnet_ids
}
the output Maps of AZ names to subnet IDs look like these
public_az_subnet_ids = {
us-east-2a = subnet-ea58d78e
us-east-2b = subnet-556ee131
us-east-2c = subnet-6f54db0b
}
private_az_subnet_ids = {
us-east-2a = subnet-376de253
us-east-2b = subnet-9e53dcfa
us-east-2c = subnet-a86fe0cc
}
and the created subnet IDs could be found by the AZ names using map["key"] or lookup(map, key, [default]),
for example:
public_az_subnet_ids["us-east-2a"]
lookup(private_az_subnet_ids, "us-east-2b")
Variables
Required Variables
availability_zones(list(string)) requiredList of Availability Zones (e.g.
['us-east-1a', 'us-east-1b', 'us-east-1c'])cidr_block(string) requiredBase CIDR block which is divided into subnet CIDR blocks (e.g.
10.0.0.0/16)vpc_id(string) requiredVPC ID
Optional Variables
az_ngw_ids(map(string)) optionalOnly for private subnets. Map of AZ names to NAT Gateway IDs that are used as default routes when creating private subnets.
You should either supply one NAT Gateway ID for each AZ invar.availability_zonesor leave the map empty.
If empty, no default egress route will be created and you will have to create your own usingaws_route.Default value:
{ }igw_id(string) optionalInternet Gateway ID that is used as a default route when creating public subnets (e.g.
igw-9c26a123)Default value:
""ipv6_cidr_block(string) optionalBase IPv6 CIDR block which is divided into /64 subnet CIDR blocks
Default value:
nullipv6_enabled(bool) optionalFlag to enable/disable IPv6 creation in public subnets
Default value:
falsemax_subnets(string) optionalMaximum number of subnets that can be created. The variable is used for CIDR blocks calculation
Default value:
"6"nat_gateway_enabled(string) optionalFlag to enable/disable NAT Gateways creation in public subnets
Default value:
"true"private_network_acl_egress(list(map(string))) optionalEgress network ACL rules
Default value:
[
{
"action": "allow",
"cidr_block": "0.0.0.0/0",
"from_port": 0,
"protocol": "-1",
"rule_no": 100,
"to_port": 0
}
]private_network_acl_id(string) optionalNetwork ACL ID that is added to the private subnets. If empty, a new ACL will be created
Default value:
""private_network_acl_ingress(list(map(string))) optionalEgress network ACL rules
Default value:
[
{
"action": "allow",
"cidr_block": "0.0.0.0/0",
"from_port": 0,
"protocol": "-1",
"rule_no": 100,
"to_port": 0
}
]public_network_acl_egress(list(map(string))) optionalEgress network ACL rules
Default value:
[
{
"action": "allow",
"cidr_block": "0.0.0.0/0",
"from_port": 0,
"protocol": "-1",
"rule_no": 100,
"to_port": 0
}
]public_network_acl_id(string) optionalNetwork ACL ID that is added to the public subnets. If empty, a new ACL will be created
Default value:
""public_network_acl_ingress(list(map(string))) optionalEgress network ACL rules
Default value:
[
{
"action": "allow",
"cidr_block": "0.0.0.0/0",
"from_port": 0,
"protocol": "-1",
"rule_no": 100,
"to_port": 0
}
]type(string) optionalType of subnets to create (
privateorpublic)Default value:
"private"
Context Variables
The following variables are defined in the context.tf file of this module and part of the terraform-null-label pattern.
context.tf file of this module and part of the terraform-null-label pattern.additional_tag_map(map(string)) optionalAdditional key-value pairs to add to each map in
tags_as_list_of_maps. Not added totagsorid.
This is for some rare cases where resources want additional configuration of tags
and therefore take a list of maps with tag key, value, and additional configuration.Required: No
Default value:
{ }attributes(list(string)) optionalID element. Additional attributes (e.g.
workersorcluster) to add toid,
in the order they appear in the list. New attributes are appended to the
end of the list. The elements of the list are joined by thedelimiter
and treated as a single ID element.Required: No
Default value:
[ ]context(any) optionalSingle object for setting entire context at once.
See description of individual variables for details.
Leave string and numeric variables asnullto use default value.
Individual variable settings (non-null) override settings in context object,
except for attributes, tags, and additional_tag_map, which are merged.Required: No
Default value:
{
"additional_tag_map": {},
"attributes": [],
"delimiter": null,
"descriptor_formats": {},
"enabled": true,
"environment": null,
"id_length_limit": null,
"label_key_case": null,
"label_order": [],
"label_value_case": null,
"labels_as_tags": [
"unset"
],
"name": null,
"namespace": null,
"regex_replace_chars": null,
"stage": null,
"tags": {},
"tenant": null
}delimiter(string) optionalDelimiter to be used between ID elements.
Defaults to-(hyphen). Set to""to use no delimiter at all.Required: No
Default value:
nulldescriptor_formats(any) optionalDescribe additional descriptors to be output in the
descriptorsoutput map.
Map of maps. Keys are names of descriptors. Values are maps of the form
\{<br/> format = string<br/> labels = list(string)<br/> \}
(Type isanyso the map values can later be enhanced to provide additional options.)
formatis a Terraform format string to be passed to theformat()function.
labelsis a list of labels, in order, to pass toformat()function.
Label values will be normalized before being passed toformat()so they will be
identical to how they appear inid.
Default is{}(descriptorsoutput will be empty).Required: No
Default value:
{ }enabled(bool) optionalSet to false to prevent the module from creating any resources
Required: NoDefault value:
nullenvironment(string) optionalID element. Usually used for region e.g. 'uw2', 'us-west-2', OR role 'prod', 'staging', 'dev', 'UAT'
Required: NoDefault value:
nullid_length_limit(number) optionalLimit
idto this many characters (minimum 6).
Set to0for unlimited length.
Set tonullfor keep the existing setting, which defaults to0.
Does not affectid_full.Required: No
Default value:
nulllabel_key_case(string) optionalControls the letter case of the
tagskeys (label names) for tags generated by this module.
Does not affect keys of tags passed in via thetagsinput.
Possible values:lower,title,upper.
Default value:title.Required: No
Default value:
nulllabel_order(list(string)) optionalThe order in which the labels (ID elements) appear in the
id.
Defaults to ["namespace", "environment", "stage", "name", "attributes"].
You can omit any of the 6 labels ("tenant" is the 6th), but at least one must be present.Required: No
Default value:
nulllabel_value_case(string) optionalControls the letter case of ID elements (labels) as included in
id,
set as tag values, and output by this module individually.
Does not affect values of tags passed in via thetagsinput.
Possible values:lower,title,upperandnone(no transformation).
Set this totitleand setdelimiterto""to yield Pascal Case IDs.
Default value:lower.Required: No
Default value:
nulllabels_as_tags(set(string)) optionalSet of labels (ID elements) to include as tags in the
tagsoutput.
Default is to include all labels.
Tags with empty values will not be included in thetagsoutput.
Set to[]to suppress all generated tags.
Notes:
The value of thenametag, if included, will be theid, not thename.
Unlike othernull-labelinputs, the initial setting oflabels_as_tagscannot be
changed in later chained modules. Attempts to change it will be silently ignored.Required: No
Default value:
[
"default"
]name(string) optionalID element. Usually the component or solution name, e.g. 'app' or 'jenkins'.
This is the only ID element not also included as atag.
The "name" tag is set to the fullidstring. There is no tag with the value of thenameinput.Required: No
Default value:
nullnamespace(string) optionalID element. Usually an abbreviation of your organization name, e.g. 'eg' or 'cp', to help ensure generated IDs are globally unique
Required: NoDefault value:
nullregex_replace_chars(string) optionalTerraform regular expression (regex) string.
Characters matching the regex will be removed from the ID elements.
If not set,"/[^a-zA-Z0-9-]/"is used to remove all characters other than hyphens, letters and digits.Required: No
Default value:
nullstage(string) optionalID element. Usually used to indicate role, e.g. 'prod', 'staging', 'source', 'build', 'test', 'deploy', 'release'
Required: NoDefault value:
nulltags(map(string)) optionalAdditional tags (e.g.
{'BusinessUnit': 'XYZ'}).
Neither the tag keys nor the tag values will be modified by this module.Required: No
Default value:
{ }tenant(string) optionalID element (Rarely used, not included by default). A customer identifier, indicating who this instance of a resource is for
Required: NoDefault value:
null
Outputs
az_ngw_idsMap of AZ names to NAT Gateway IDs (only for public subnets)
az_route_table_idsMap of AZ names to Route Table IDs
az_subnet_arnsMap of AZ names to subnet ARNs
az_subnet_cidr_blocksMap of AZ names to subnet CIDR blocks
az_subnet_idsMap of AZ names to subnet IDs
az_subnet_ipv6_cidr_blocksMap of AZ names to subnet IPv6 CIDR blocks
az_subnet_mapMap of AZ names to map of information about subnets
Dependencies
Requirements
terraform, version:>= 0.13.0aws, version:>= 3.0local, version:>= 1.2null, version:>= 2.0
Providers
aws, version:>= 3.0
Modules
| Name | Version | Source | Description |
|---|---|---|---|
private_label | 0.24.1 | cloudposse/label/null | n/a |
public_label | 0.24.1 | cloudposse/label/null | n/a |
this | 0.25.0 | cloudposse/label/null | n/a |
Resources
The following resources are used by this module:
aws_eip.public(resource)aws_nat_gateway.public(resource)aws_network_acl.private(resource)aws_network_acl.public(resource)aws_route.default(resource)aws_route.public(resource)aws_route.public_ipv6(resource)aws_route_table.private(resource)aws_route_table.public(resource)aws_route_table_association.private(resource)aws_route_table_association.public(resource)aws_subnet.private(resource)aws_subnet.public(resource)
Data Sources
The following data sources are used by this module: