Module: tfstate-backend
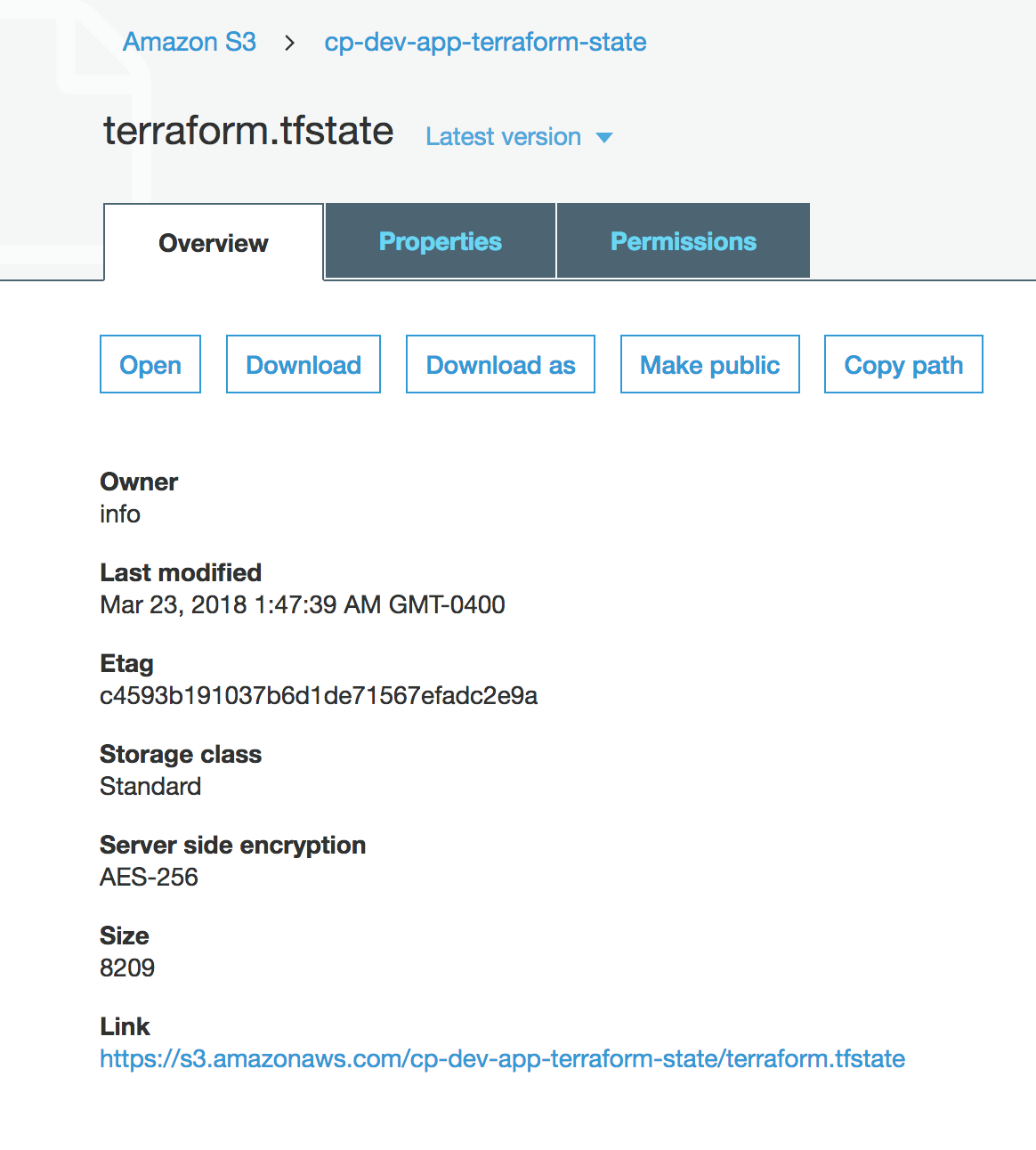
Terraform module to provision an S3 bucket to store terraform.tfstate file and a DynamoDB table to lock the state file
to prevent concurrent modifications and state corruption.
The module supports the following:
- Forced server-side encryption at rest for the S3 bucket
- S3 bucket versioning to allow for Terraform state recovery in the case of accidental deletions and human errors
- State locking and consistency checking via DynamoDB table to prevent concurrent operations
- DynamoDB server-side encryption
https://www.terraform.io/docs/backends/types/s3.html
NOTE: The operators of the module (IAM Users) must have permissions to create S3 buckets and DynamoDB tables when performing terraform plan and terraform apply
NOTE: This module cannot be used to apply changes to the mfa_delete feature of the bucket. Changes regarding mfa_delete can only be made manually using the root credentials with MFA of the AWS Account where the bucket resides. Please see: https://github.com/terraform-providers/terraform-provider-aws/issues/629
Usage
Create
Follow this procedure just once to create your deployment.
-
Add the
terraform_state_backendmodule to yourmain.tffile. The comment will help you remember to follow this procedure in the future:# You cannot create a new backend by simply defining this and then
# immediately proceeding to "terraform apply". The S3 backend must
# be bootstrapped according to the simple yet essential procedure in
# https://github.com/cloudposse/terraform-aws-tfstate-backend#usage
module "terraform_state_backend" {
source = "cloudposse/tfstate-backend/aws"
# Cloud Posse recommends pinning every module to a specific version
# version = "x.x.x"
namespace = "eg"
stage = "test"
name = "terraform"
attributes = ["state"]
terraform_backend_config_file_path = "."
terraform_backend_config_file_name = "backend.tf"
force_destroy = false
}
# Your Terraform configuration
module "another_module" {
source = "....."
}Module inputs
terraform_backend_config_file_pathandterraform_backend_config_file_namecontrol the name of the backend definition file. Note that whenterraform_backend_config_file_pathis empty (the default), no file is created. -
terraform init. This downloads Terraform modules and providers. -
terraform apply -auto-approve. This creates the state bucket and DynamoDB locking table, along with anything else you have defined in your*.tffile(s). At this point, the Terraform state is still stored locally.Module
terraform_state_backendalso creates a newbackend.tffile that defines the S3 state backend. For example:backend "s3" {
region = "us-east-1"
bucket = "< the name of the S3 state bucket >"
key = "terraform.tfstate"
dynamodb_table = "< the name of the DynamoDB locking table >"
profile = ""
role_arn = ""
encrypt = true
}Henceforth, Terraform will also read this newly-created backend definition file.
-
terraform init -force-copy. Terraform detects that you want to move your Terraform state to the S3 backend, and it does so per-auto-approve. Now the state is stored in the S3 bucket, and the DynamoDB table will be used to lock the state to prevent concurrent modification.
This concludes the one-time preparation. Now you can extend and modify your Terraform configuration as usual.
Destroy
Follow this procedure to delete your deployment.
- In
main.tf, change theterraform_state_backendmodule arguments as follows:module "terraform_state_backend" {
# ...
terraform_backend_config_file_path = ""
force_destroy = true
} terraform apply -target module.terraform_state_backend -auto-approve. This implements the above modifications by deleting thebackend.tffile and enabling deletion of the S3 state bucket.terraform init -force-copy. Terraform detects that you want to move your Terraform state from the S3 backend to local files, and it does so per-auto-approve. Now the state is once again stored locally and the S3 state bucket can be safely deleted.terraform destroy. This deletes all resources in your deployment.- Examine local state file
terraform.tfstateto verify that it contains no resources.
Bucket Replication (Disaster Recovery)
To enable S3 bucket replication in this module, set s3_replication_enabled to true and populate s3_replica_bucket_arn with the ARN of an existing bucket.
module "terraform_state_backend" {
source = "cloudposse/tfstate-backend/aws"
# Cloud Posse recommends pinning every module to a specific version
# version = "x.x.x"
namespace = "eg"
stage = "test"
name = "terraform"
attributes = ["state"]
terraform_backend_config_file_path = "."
terraform_backend_config_file_name = "backend.tf"
force_destroy = false
s3_replication_enabled = true
s3_replica_bucket_arn = "arn:aws:s3:::eg-test-terraform-tfstate-replica"
}
Variables
Required Variables
Optional Variables
acl(string) optionalThe canned ACL to apply to the S3 bucket
Default value:
"private"arn_format(string) optionalARN format to be used. May be changed to support deployment in GovCloud/China regions.
Default value:
"arn:aws"billing_mode(string) optionalDynamoDB billing mode
Default value:
"PAY_PER_REQUEST"block_public_acls(bool) optionalWhether Amazon S3 should block public ACLs for this bucket
Default value:
trueblock_public_policy(bool) optionalWhether Amazon S3 should block public bucket policies for this bucket
Default value:
truebucket_enabled(bool) optionalWhether to create the S3 bucket.
Default value:
truebucket_ownership_enforced_enabled(bool) optionalSet bucket object ownership to "BucketOwnerEnforced". Disables ACLs.
Default value:
truedeletion_protection_enabled(bool) optionalA boolean that enables deletion protection for DynamoDB table
Default value:
falsedynamodb_enabled(bool) optionalWhether to create the DynamoDB table for state locking. Note: DynamoDB-based locking is deprecated in Terraform >= 1.10 in favor of S3 native locking (s3_state_lock_enabled). See https://developer.hashicorp.com/terraform/language/backend/s3#enabling-dynamodb-state-locking-deprecated
Default value:
truedynamodb_table_name(string) optionalOverride the name of the DynamoDB table which defaults to using
module.dynamodb_table_label.idDefault value:
nullenable_point_in_time_recovery(bool) optionalEnable DynamoDB point-in-time recovery
Default value:
trueenable_public_access_block(bool) optionalEnable Bucket Public Access Block
Default value:
trueforce_destroy(bool) optionalA boolean that indicates the S3 bucket can be destroyed even if it contains objects. These objects are not recoverable
Default value:
falseignore_public_acls(bool) optionalWhether Amazon S3 should ignore public ACLs for this bucket
Default value:
truekms_master_key_id(string) optionalAWS KMS master key ID used for the SSE-KMS encryption.
This can only be used when you set the value of sse_algorithm as aws:kms.Default value:
nullloggingoptionalDestination (S3 bucket name and prefix) for S3 Server Access Logs for the S3 bucket.
Type:
list(object({
target_bucket = string
target_prefix = string
}))Default value:
[ ]mfa_delete(bool) optionalA boolean that indicates that versions of S3 objects can only be deleted with MFA. ( Terraform cannot apply changes of this value; https://github.com/terraform-providers/terraform-provider-aws/issues/629 )
Default value:
falsepermissions_boundary(string) optionalARN of the policy that is used to set the permissions boundary for the IAM replication role
Default value:
""prevent_unencrypted_uploads(bool) optionalPrevent uploads of unencrypted objects to S3
Default value:
trueprofile(string) optionalAWS profile name as set in the shared credentials file
Default value:
""read_capacity(number) optionalDynamoDB read capacity units when using provisioned mode
Default value:
5restrict_public_buckets(bool) optionalWhether Amazon S3 should restrict public bucket policies for this bucket
Default value:
truerole_arn(string) optionalThe role to be assumed
Default value:
""s3_bucket_name(string) optionalS3 bucket name. If not provided, the name will be generated from the context by the label module.
Default value:
""s3_replica_bucket_arn(string) optionalThe ARN of the S3 replica bucket (destination)
Default value:
""s3_replication_enabled(bool) optionalSet this to true and specify
s3_replica_bucket_arnto enable replicationDefault value:
falses3_state_lock_enabled(bool) optionalWhether to use S3 native state locking (use_lockfile). Requires Terraform >= 1.10. When enabled, DynamoDB is not needed for state locking. See https://developer.hashicorp.com/terraform/language/backend/s3#s3-state-locking
Default value:
falsesource_policy_documents(list(string)) optionalList of IAM policy documents (in JSON format) that are merged together into the generated S3 bucket policy.
Statements must have unique SIDs.
Statement having SIDs that match policy SIDs generated by this module will override them.Default value:
[ ]sse_encryption(string) optionalThe server-side encryption algorithm to use.
Valid values areAES256,aws:kms, andaws:kms:dsse.Default value:
"AES256"terraform_backend_config_file_name(string) optional(Deprecated) Name of terraform backend config file to generate
Default value:
"terraform.tf"terraform_backend_config_file_path(string) optional(Deprecated) Directory for the terraform backend config file, usually
.. The default is to create no file.Default value:
""terraform_backend_config_template_file(string) optional(Deprecated) The path to the template used to generate the config file
Default value:
""terraform_state_file(string) optionalThe path to the state file inside the bucket
Default value:
"terraform.tfstate"terraform_version(string) optionalThe minimum required terraform version
Default value:
nullwrite_capacity(number) optionalDynamoDB write capacity units when using provisioned mode
Default value:
5
Context Variables
The following variables are defined in the context.tf file of this module and part of the terraform-null-label pattern.
context.tf file of this module and part of the terraform-null-label pattern.additional_tag_map(map(string)) optionalAdditional key-value pairs to add to each map in
tags_as_list_of_maps. Not added totagsorid.
This is for some rare cases where resources want additional configuration of tags
and therefore take a list of maps with tag key, value, and additional configuration.Required: No
Default value:
{ }attributes(list(string)) optionalID element. Additional attributes (e.g.
workersorcluster) to add toid,
in the order they appear in the list. New attributes are appended to the
end of the list. The elements of the list are joined by thedelimiter
and treated as a single ID element.Required: No
Default value:
[ ]context(any) optionalSingle object for setting entire context at once.
See description of individual variables for details.
Leave string and numeric variables asnullto use default value.
Individual variable settings (non-null) override settings in context object,
except for attributes, tags, and additional_tag_map, which are merged.Required: No
Default value:
{
"additional_tag_map": {},
"attributes": [],
"delimiter": null,
"descriptor_formats": {},
"enabled": true,
"environment": null,
"id_length_limit": null,
"label_key_case": null,
"label_order": [],
"label_value_case": null,
"labels_as_tags": [
"unset"
],
"name": null,
"namespace": null,
"regex_replace_chars": null,
"stage": null,
"tags": {},
"tenant": null
}delimiter(string) optionalDelimiter to be used between ID elements.
Defaults to-(hyphen). Set to""to use no delimiter at all.Required: No
Default value:
nulldescriptor_formats(any) optionalDescribe additional descriptors to be output in the
descriptorsoutput map.
Map of maps. Keys are names of descriptors. Values are maps of the form
\{<br/> format = string<br/> labels = list(string)<br/> \}
(Type isanyso the map values can later be enhanced to provide additional options.)
formatis a Terraform format string to be passed to theformat()function.
labelsis a list of labels, in order, to pass toformat()function.
Label values will be normalized before being passed toformat()so they will be
identical to how they appear inid.
Default is{}(descriptorsoutput will be empty).Required: No
Default value:
{ }enabled(bool) optionalSet to false to prevent the module from creating any resources
Required: NoDefault value:
nullenvironment(string) optionalID element. Usually used for region e.g. 'uw2', 'us-west-2', OR role 'prod', 'staging', 'dev', 'UAT'
Required: NoDefault value:
nullid_length_limit(number) optionalLimit
idto this many characters (minimum 6).
Set to0for unlimited length.
Set tonullfor keep the existing setting, which defaults to0.
Does not affectid_full.Required: No
Default value:
nulllabel_key_case(string) optionalControls the letter case of the
tagskeys (label names) for tags generated by this module.
Does not affect keys of tags passed in via thetagsinput.
Possible values:lower,title,upper.
Default value:title.Required: No
Default value:
nulllabel_order(list(string)) optionalThe order in which the labels (ID elements) appear in the
id.
Defaults to ["namespace", "environment", "stage", "name", "attributes"].
You can omit any of the 6 labels ("tenant" is the 6th), but at least one must be present.Required: No
Default value:
nulllabel_value_case(string) optionalControls the letter case of ID elements (labels) as included in
id,
set as tag values, and output by this module individually.
Does not affect values of tags passed in via thetagsinput.
Possible values:lower,title,upperandnone(no transformation).
Set this totitleand setdelimiterto""to yield Pascal Case IDs.
Default value:lower.Required: No
Default value:
nulllabels_as_tags(set(string)) optionalSet of labels (ID elements) to include as tags in the
tagsoutput.
Default is to include all labels.
Tags with empty values will not be included in thetagsoutput.
Set to[]to suppress all generated tags.
Notes:
The value of thenametag, if included, will be theid, not thename.
Unlike othernull-labelinputs, the initial setting oflabels_as_tagscannot be
changed in later chained modules. Attempts to change it will be silently ignored.Required: No
Default value:
[
"default"
]name(string) optionalID element. Usually the component or solution name, e.g. 'app' or 'jenkins'.
This is the only ID element not also included as atag.
The "name" tag is set to the fullidstring. There is no tag with the value of thenameinput.Required: No
Default value:
nullnamespace(string) optionalID element. Usually an abbreviation of your organization name, e.g. 'eg' or 'cp', to help ensure generated IDs are globally unique
Required: NoDefault value:
nullregex_replace_chars(string) optionalTerraform regular expression (regex) string.
Characters matching the regex will be removed from the ID elements.
If not set,"/[^a-zA-Z0-9-]/"is used to remove all characters other than hyphens, letters and digits.Required: No
Default value:
nullstage(string) optionalID element. Usually used to indicate role, e.g. 'prod', 'staging', 'source', 'build', 'test', 'deploy', 'release'
Required: NoDefault value:
nulltags(map(string)) optionalAdditional tags (e.g.
{'BusinessUnit': 'XYZ'}).
Neither the tag keys nor the tag values will be modified by this module.Required: No
Default value:
{ }tenant(string) optionalID element (Rarely used, not included by default). A customer identifier, indicating who this instance of a resource is for
Required: NoDefault value:
null
Outputs
dynamodb_table_arnDynamoDB table ARN
dynamodb_table_idDynamoDB table ID
dynamodb_table_nameDynamoDB table name
s3_bucket_arnS3 bucket ARN
s3_bucket_domain_nameS3 bucket domain name
s3_bucket_idS3 bucket ID
s3_replication_role_arnThe ARN of the IAM Role created for replication, if enabled.
terraform_backend_configRendered Terraform backend config file
Dependencies
Requirements
terraform, version:>= 1.1.0aws, version:>= 6.0.0local, version:>= 2.0time, version:>= 0.7.1
Providers
aws, version:>= 6.0.0local, version:>= 2.0time, version:>= 0.7.1
Modules
| Name | Version | Source | Description |
|---|---|---|---|
bucket_label | 0.25.0 | cloudposse/label/null | n/a |
dynamodb_table_label | 0.25.0 | cloudposse/label/null | n/a |
replication_label | 0.25.0 | cloudposse/label/null | n/a |
this | 0.25.0 | cloudposse/label/null | n/a |
Resources
The following resources are used by this module:
aws_dynamodb_table.with_server_side_encryption(resource)aws_iam_policy.replication(resource)aws_iam_role.replication(resource)aws_iam_role_policy_attachment.replication(resource)aws_s3_bucket.default(resource)aws_s3_bucket_acl.default(resource)aws_s3_bucket_logging.default(resource)aws_s3_bucket_object_lock_configuration.default(resource)aws_s3_bucket_ownership_controls.default(resource)aws_s3_bucket_policy.default(resource)aws_s3_bucket_public_access_block.default(resource)aws_s3_bucket_replication_configuration.replication(resource)aws_s3_bucket_server_side_encryption_configuration.default(resource)aws_s3_bucket_versioning.default(resource)local_file.terraform_backend_config(resource)time_sleep.wait_for_aws_s3_bucket_settings(resource)
Data Sources
The following data sources are used by this module:
aws_iam_policy_document.aggregated_policy(data source)aws_iam_policy_document.bucket_policy(data source)aws_iam_policy_document.replication(data source)aws_iam_policy_document.replication_sts(data source)aws_region.current(data source)